✔ Quick Summary: A lock stops the honest and slows the impatient, but it offers zero protection against a predator operating in the gray area. This guide focuses on reclaiming your boundaries by documenting the initial testing of your boundaries and the normalization of deviance in behavior. By logging these patterns, you bridge the gaslight gap. This is the hollow space where police dismiss your crisis as a civil matter and authorities ignore systematic harassment. Whether you are facing threats to your livelihood, your property, or your personal safety, you will learn to replace unproductive confrontation with a silent, documented strategy that the system cannot easily ignore.
The Deadbolt Delusion: Why You’re Currently an Easy Mark
You were taught that if you follow the rules, the rules will protect you. If you’re a good person, and you do the right thing, that good things will come your way.
This dangerous set of assumptions is nothing more than a warm blanket stitched with a false sense of security.
I’m not trying to hype your fear or make you paranoid.
Predators do not play by your rules, your pastor’s guidelines, or the assurances underpinned by your neighborhood community watch group.
Predators do not care about criminal law. If they did, they wouldn’t break the law.
This is true regardless of their intent:
- To rob you as you walk down the street
- Break into your home
- “Convince you” to continue spending time together
- Steal your vehicle (with or without you still in it)
- Swipe the cargo from your 53′ trailer
The deadbolt you lock every time you come home, the solid door that separates you from outside world, the seatbelts you wrap through the door before crawling into your sleeper, and a clean conscience offers hope and comfort.
That all shatters the second the glass does.
✔ Predators do not care about the meaning of the word “No,” regardless of their background, age, or intent.
Assessing Threat Motive: Why Tactical Readiness Trumps Mechanical Deterrents
A lock is a mechanical deterrent. It stops the honest and slows down the impatient.
Locks do nothing against a stalker that knows your daily schedule.
They do nothing against a bully who uses plausible deniability as a weapon.
When your physical space is being invaded (whether that space is your home, your vehicle, or your mental health) you are in a fight.
Most crime takes place before the HR department believes you, your trucking company agrees to change your load, the principal can pin down the bully, or law-enforcement arrives to assist.
Victims are often left to bewildered, in shock, sometimes physically harmed, and left to deal with an aftermath of financial loss, mental trauma, medical bills, and lost wages due to taking time off work to deal with all of the administrative things they are now responsible for simply because someone else made the choice to break the law.
A martial arts teacher once told me, “Common sense before self-defense.”
What my sensei did not teach me is how to assess the intent levels of a person’s threats outside of imminent physical attack.
⚠️ Calculated perpetrators work in the gray area on purpose. They do just enough to get at you, without actually breaking a law. These are some of the most dangerous people to work with.
These individuals can be:
- members/ex-members of your family
- former romantic interests
- a stalker
- someone in your HR department
- a toxic boss
- a power-tripping driver leader
- a member of the clergy
- a lawyer
- a doctor
- a teacher
- a bully
- a police officer
Basically, anyone who feels they have an ax to grind regardless of the authority level they can legally wield.
✔ Their reasons do not have to be real in actually (or to most sane, normal individuals), but they are real to the perpetrator(s) involved in the offense(s).
Trying to understand what’s going on in the mind of the person intent on hurting you, is key to helping you bolster your safety. Without it, you might be trying to do all the right things to keep yourself physically safe, while ignoring how far the other person is willing to go to inflict you harm or the level of harm they are willing to inflict.
Turning a blind eye to these possibilities is a luxury you can’t afford.
Staring at the reality of human malice is gut-wrenching (and can feel very far-fetched), especially when the idea of someone you once shared a meal with or a life with, begins systematically gutting your future with the sudden pleasure and precision of a psychopath.
An innocent mind, the mind that follows all the right rules, dismisses these things seem impossible. The possibility of a “good” person now trying to harm them feels illogical and is very difficult to reconcile.
And that’s exactly what the perpetrator is counting on.
Ignoring it hands the predator a massive head start.
Strategic Hardening: Balancing Mechanical Deterrents with Perpetrator Motive and Documentation
The systems put in place to protect you are not primarily designed to be proactive. The legal and law-enforcement systems are mainly reactive, only looking to assist you if there is an eminent threat, if you’ve already been harmed, or if there is a “enough” red flags according to their policies to warrant assistance.
Unfortunately, those definitions do not match up to the multi-faceted unsafe realities that many face daily.
Not every jurisdiction has legal or law-enforcement personnel that takes early reporting seriously enough.
Just because the legal or law-enforcement systems does not agree that someone is trying to hurt you does not mean that your attacker is not trying to hurt you or will stop trying your attacker has achieved their goal.
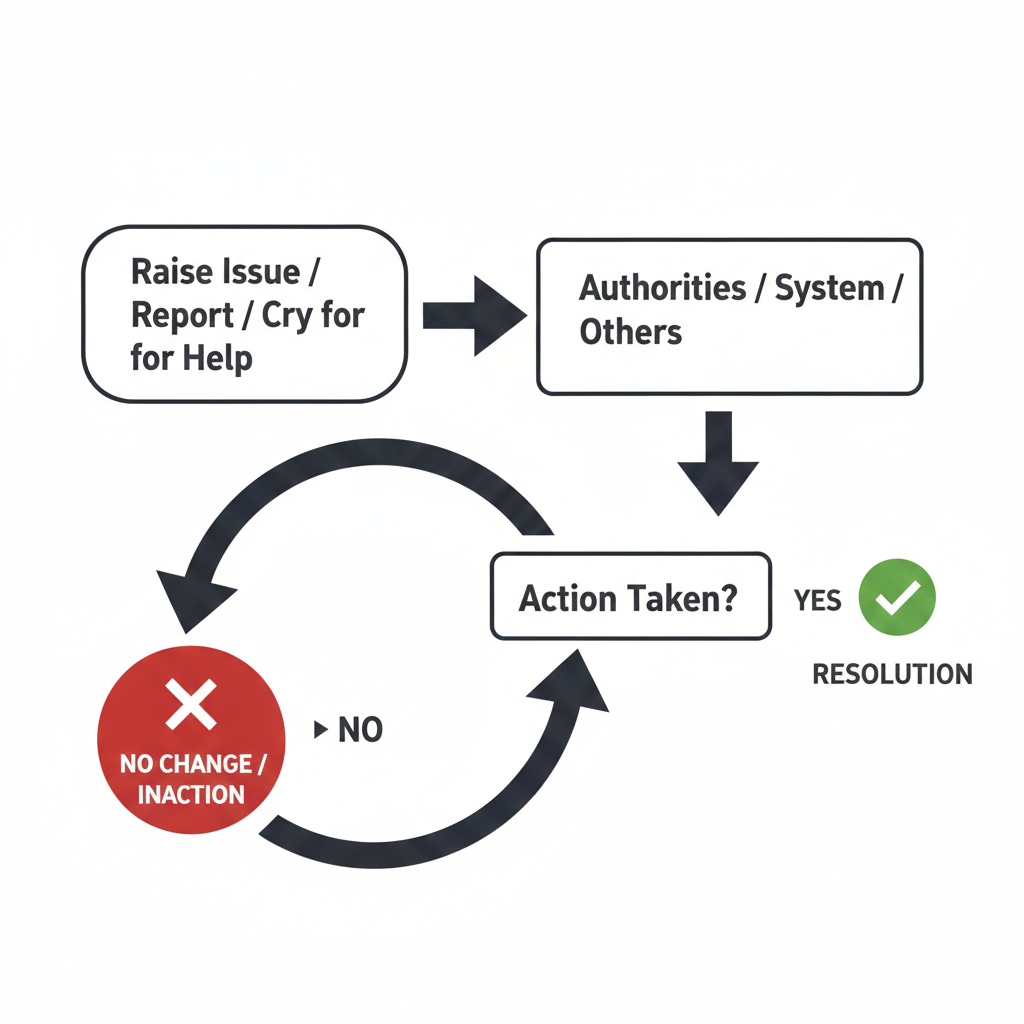
Often times, you’ll raise an issue by reporting something to the appropriate authorities, and then nothing is truly done about it.
Some systems and agencies will actually call you out for potentially ruining the reputation of another person simply because you spoke up.
They’re more interested in protecting comfortable feelings than they are in investigating certain complaints.
That’s why you have to balance three things to stay physically safe:
- Mechanical Deterrents: Think physical barriers like locks, security cameras, bracer bars under door knobs, security systems, small hand-held weapons (ones that are legal in your jurisdiction), and active situational awareness. They buy you time, but they do not buy you safety in all cases. They are part of the first layer, designed to filter out the opportunistic thief, and make things harder for the dedicated predator.
- Perpetrator Motive: You must look past the lock and see the intent. Is this a random act of desperation, or is this a calculated move by someone who knows you? Understanding the “Why” behind the threat allows you to adjust your posture. A stalker requires a different defensive strategy than a common burglar. While examining this, you must remember, that their motive is not required to be “logical” to you, only to them.
- The Evidence Log: This is the most critical and most ignored layer. The moment you’re threatened or a mechanical deterrent is challenged, the clock starts on your legal defense. Documenting the breach including the time, weather, what you were doing when it happened, and possible motives, turns a physical violation into a documented fact that systems can start to acknowledge.
If you show up with feelings and fears, you are a nuisance.
If you show up with a paper trail of verifiable data, you show up with a polite request (with teeth), respectfully “asking” authorities to listen.
The Five Fronts of Physical Encroachment
Physical defense isn’t just about a fistfight, a shouting match, or TikTok scripts. It is about the systematic reclamation of your boundaries. Here is how you’re being hunted on the five primary fronts, and how your records can become your shield.
The Stalker: Ending the Silent Surveillance
Stalking is a psychological game played by people who rely on your silence and your good intentions.
They count on you being too polite to make a scene, too worried about your reputation at your job to ask for help, and too upset to document their infractions.
- The Problem: Deleting the “weird” texts or ignoring the third time you saw that silver SUV. You think you’re overreacting if you keep track of the information, making too much of a fuss, or being paranoid. You’re actually making yourself an easier target.
- The Tactical Push Back: Every sighting is a data point. Three sightings in 48 hours isn’t a coincidence. Anything more than twice, especially in cases where you have asked a person to stop, is a pattern of escalation. When you hand a timeline to an officer that shows a deliberate sequence that can be verified through camera footage of some kind (think body cam, dash cam, or the ATM camera footage from across the street) or other verification methods, you aren’t complaining. Authorities often prefer proof if you have it. This both helps comply with their preferences and build a case to protect yourself.
Bullying: Piercing the Professional Gaslight
Whether it’s in an office or a neighborhood, bullies win because they operate in the gray area. They make small, deniable comments or straight up tell you that what you’re remembering “never happened,” and often do it with a face that easily convinces bystanders.
- The Problem: They push until you snap, then use your legitimate reaction as proof that you are the problem.
- The Tactical Push Back: You stop reacting and start recording. Use the 19 fields on the Entry Log Form to document each instance. When you present a 30-day log of systematic harassment, you’ve just built a wall that no HR department can legally ignore without exposing themselves to a possible lawsuit.
Personal Security & Defense: The Home Front
If someone is harassing you at your home, your cameras are only as good as the log that accompanies them.
- The Problem: A group of people on video standing on your sidewalk is in a “public space.” You can’t ask them to not violate their rights by not standing on a sidewalk.
- The Pattern: A video of that same group of people standing there every Tuesday at 2 a.m. for three weeks looking directly at your home making hand shapes like a pointing gun directly at your living room window (cross-referenced in your Paper Trail Table of Contents) is a provable (and escalating) pattern worth investigating.
Road Rage: The High-Stakes Target
Road rage happens because people think they are anonymous behind a windshield.
- The Problem: There’s a lot of traffic with several people darting in an out of lanes. This is all caught on your dash cam “just in case.” To some people (possibly a jury panel) that resembles every day, typical rush-hour traffic in your city. They can see one red car that keeps popping in an out of your view. The jury decides the red card is being driven by another citizen that cannot drive, but cannot be convinced of intent to harm you.
- The Tactical View: If you are being followed or intimidated on the road, your phone can dial for emergency help (if you have sufficient cell signal) or your dash cam (if it’s working properly in that moment) isn’t enough. You need to be able to document the make, model, license, the specific aggressive maneuvers if possible, and the time span it occurred. One sharp lane change during traffic is not necessarily road rage. Consistent erratic behavior aimed at you (and not other drivers) over a several minutes shows abnormal behavior.
Commercial Driving: A Corporate Starvation Trap
If you drive a truck, a school bus, or a corporate delivery van over a certain size, you are governed by the Federal Motor Carrier Safety Administration (FMCSA).
This organization is a lead agency within the U.S. Department of Transportation. Their primary task is to prevent, investigate, and uphold standards that lower accidents, death, or injuries caused by large commercial vehicles. To do that, it makes professional commercial drivers follow several highly regulated rule sets.
- The Conflict: You report a safety issue (a small leak, questionable brakes, a bald or slightly under inflated tire, a bent bar, or forced dispatch that violates hours of service, for example.) The company can’t fire you because the law has it baked in that they can’t. You both know this.
- The Retaliation: They “starve” you for miles, give you junk loads, or put you on routes or delivery locations where you have a higher chance of getting into an accident because of your possible inexperience in that specific type of maneuver. They cut your miles from 1,900 a week to 300. When you ask why, they blame “the market” or “logistics.”
- The Weapon: You must log every safety report you make, the issues you reported, who you reported it to, and all the events that take place afterward, even if its a few months later. (If you need a starting place to make this easy, try using the Paper Trail Primer.) This can look like documenting a soon-after drop in your mileage, being written up for small things that in the past were previously looked over, poor performance reviews, or administrative verbal or written warnings.
You are documenting facts which helps others see the correlation, especially if the person reviewing your information has significant experience in the trucking or transportation industry. Showing that your miles dropped 40% the week after you reported a mechanical failure doesn’t make you a disgruntled driver.
You’re using the details you’re asked to manage daily (miles, trip planning, pre-trip and post-trip inspections, etc., to document a pattern.
These patterns become very interesting to those in charge of issuing fines or sanctions.
The Anatomy of Encroachment: How You Lose Your Space
Personal security is not usually lost in a single, explosive moment. It’s eroded through disagreements, unexpected and harsh behaviors from others, or uncalled for threats.
A perpetrator doesn’t wake up and decide to dismantle your life. When they’ve chosen you for a mark, they take it from you in stages, watching to see if you’re paying attention.
If you don’t recognize the sequence, you can’t interrupt the outcome until it’s too late.
The Baseline: The Quiet Before the Breach
Every environment has a “normal.” Think the predictable rhythm of your neighborhood, the standard professional tone of your office, or the routine of your routes. These are baselines.
Baselines become dangerous because they breed complacency. You assume that because things were safe yesterday, they are safe today. You stop looking at the perimeter of your yard. You stop checking the details of seals on your trailer with a critical eye. You settle into the “good person” assumption that the world is inherently stable.
Normal fades into the background, and you rest comfortably on autopilot, oblivious to subtle threats and subtle danger.
If things feel good, calm, stable, or peaceful, look up and scan your surroundings. It doesn’t have to break your peace, but it should scratch your comfort levels slightly.
The Testing Phase: Throwing Pebbles
A predator starts by “throwing pebbles” to test the depth of your boundaries. These are small, easily dismissed infractions designed to see if you’ll document them, report them, cry about them on social media, or if you’ll be nice and let them slide.
- The neighbor who “accidentally” walks ten feet onto your property to retrieve a ball when no one was outside playing ball previously.
- The boss who sends a “quick question” text five hours after your shift ended.
- The stranger who lingers just a second too long at the driver-side window of your truck.
- Someone who begins to yell at you in pubic, falsely accusing you of doing something you didn’t do.
If you confront them at all, they might paint you as overreactive or “crazy.” They’ll reply with things like, “Cool it, man/lady. I was just playin’,” or “No need to get upset.“
They’re counting on you to care about your reputation in that moment and what others around you think of you to avoid embarrassment. This behavior is designed to make you back off and let them have them the last word, or at the very least, escape the situation and get away with whatever pebbles they just threw, leaving you to clean up the mess.
In your mind, these are isolated incidents. To the perpetrator, these are data points. They are measuring your politeness threshold.
If you don’t log the pebble back, and fast, they know they can move on to the brick.
Log the pebble back with records instead of physical confrontation.
The Normalization of Deviance: Your New (Dangerous) Reality
This is the psychological trap where you start accepting abnormal behavior as “just the way things are.” You stop being shocked by the encroachment and start adapting to it.
- You start walking on emotional eggshells when you go to work and don’t know why. At first it bothers you. Later, it blends into “that’s just how Bob is. I’ll find another job later.”
- You internally brace for “impact” when you’re about to speak to your neighbor, not knowing how they will react. Later, you don’t speak to the neighbor much, but you’ve noticed you have more headaches when thinking about doing yard work or being in situations where you could run into your neighbor.
When you normalize deviance, you stop seeing the threat as a problem to block or stop. You accept that this is just the way things are.
This is exactly where the predator wants you: quiet, adapted, and undocumented.
In extreme cases, the predator doesn’t care how much documentation you have because part of their plan is to lean on other “enforcers” to stop you from crying about it. For examples, think about documented geo-political issues in which one country puts pressure on the leaders of another to portray poor behavior in the media in certain specific ways.
The Leverage Point: The Power Move they Live For
Eventually, the perpetrator reaches the leverage point. They’ve tested your boundaries, normalized their presence in your space, and confirmed that you haven’t been keeping record of the “pebbles.”
This is when the harassment turns into a lawsuit (and if you don’t have your prevention folder ready, you’ve already lost), the grumpy boss turns into a termination letter, or the curious/kind/polite “caring” neighbor turns into a physical intruder. They move in for a dominant power move because they realize you have no real history or proof to back up your current claims. Your perpetrator expects at this point, that you’ll allow them to continue. They get a high from wielding fake power in this manner, even when they’re technically breaking the law.
When you finally call for help, you end up describing, what looks like to outsiders, a “sudden” escalation. But without a log of the testing phase, the system sees it as a one-time event, or worse, a “misunderstanding.” By the time the leverage point is reached, the lack of records has already handed them the win.
The Gaslight Gap: The System is Designed to Ignore You
There is a hollow space between the moment you realize you’re in danger and the moment the “authorities” decide to do something about it. I call this the “gaslight gap.” It’s the period where you’re told your intuition is wrong, your fears are overblown, and your problem isn’t “their problem.”
If you don’t have a record to bridge this gap, your sense of sanity can fall right in and may never come back out.
The Civil Matter Trap: The Police Officer’s Exit Strategy
“Sorry, this is a civil matter.”
If you’ve heard these six words, you know the sinking feeling of being abandoned. It’s the phrase used by law enforcement to avoid the paperwork of a situation that hasn’t yet resulted in a measurable crime.
- The Trap: When a neighbor repeatedly shines a high-powered spotlight into your bedroom at 3 a.m., the police don’t see a property dispute. They see a “civil matter.”
- The Record Fix: Your stack of Entry Log Forms turns a “civil matter” into a measurable pattern of possible criminal behavior. Instead of reporting a general complaint that you’re having difficulty explaining in the presence of a police officer, you present a 45-day timeline showing systematic, targeted sleep deprivation. When you move the conversation from what happened once to what is happening consistently with measurable proof, you take away their excuse to look away.
The “He-Said, She-Said” Fallacy: Filling the Vacuum
Predators thrive in a vacuum. When there is no objective record of an event, the system defaults to whoever tells the more convincing story. This is the “He-Said, She-Said” fallacy, and it’s a game you will almost always lose if you’re playing from a place of trauma.
✔ Most people get crushed in family court because even though they have the truth, they don’t have the documentation organized in a way for legal professionals to see or find the facts.
A lack of documentation creates an empty space.
A calculated perpetrator will fill that space with a narrative that makes you look like the aggressor, the “crazy” ex, or the “difficult” employee. By the time you’re standing in front of a judge or an HR director, the predator’s lies have had weeks to settle into the foundation of the case.
Your records act as a physical barrier that cracks the narrative your perpetrator created and fed.
Proper records fill the vacuum with dates, times, and specific descriptions that lies cannot penetrate.
You don’t have to be convincing when you have an organized body of documentation. The paper does the talking for you.
The Cost of Silence: The Tax You Pay for Waiting
Waiting for the system to care is an expensive gamble. There is a tangible tax on your silence, and it’s paid in two ways:
- The Financial Tax: This is the cost of the aftermath. It’s the legal fees you’ll pay to a lawyer to discover evidence that you should have been carefully logging all along. It’s the lost wages from the days you can’t work because the stress has finally crashed your nervous system or because of court dates. You need to understand why “good intentions” aren’t enough when the system starts looking at your life through a legal lens.
- The Physical Tax: This is the toll on your body. When you stay in a state of hyper-vigilance without an outlet, your body stays “on.” The stress isn’t just in your head, as the doctors wish it was. No, it’s taking up residence in your gut, your heart, and your sleep cycles.
Ignoring encroachment doesn’t make it stop. It just makes the eventual collision more expensive and more damaging. The Paper Trail Primer helps stop the tax from draining you emotionally and mentally dry before you even get to court.
Drawing the Line: Moving from Reaction to Documentation
If you’ve been following the “good person” rules, your instinct is to explain, to reason, or to “set things straight” with the person encroaching on your space. You think if you just show them how much they are hurting you, they’ll stop.
They won’t.
For the calculated perpetrator, your explanation is a roadmap showing them exactly where to find your soft spots.
The Myth of the Productive Confrontation
When you confront a stalker, a bully, or a toxic superior, you are handing them exactly what they want: Engagement.
Whether you are screaming or pleading, you are giving them your time and your energy. You are also creating a “he-said, she-said” event that has no objective witness.
If you choose to engage, you are essentially erasing the work of your documentation as the system views the conflict as “mutual drama” rather than a one-sided encroachment.
The Silent Defense: Closing the Loop
Instead of a confrontation, you implement a hard boundary.
This isn’t for them, and at first, isn’t even for the courts, the HR department, or the police.
In the beginning, it’s for your records and the reclaiming of your feelings of safety and mental sanity.
- The Final Communication: If safe and appropriate, a single, clear, and documented statement is all that is required: “Do not contact me again in any way. Do not come to my property. Any further contact will be recorded and reported.”
- The Total Blackout: After that statement, you stop. You don’t answer the “Why?” texts. You don’t respond to the “accidental” driveway turn-arounds. Every attempt they make after this point is no longer a “misunderstanding.” No, after this point, it is a documented violation of a clear boundary. And you must treat it this way. You are not being “mean” by doing so. You’re being safe. You’re protecting yourself and your family in ways that most people count on outside agencies or authorities to do.
- The Documentation Shift: This is where your Evidence Log Form becomes your primary voice. Every time they reach across that line, you aren’t “dealing with it,” you are collecting it with 19 unemotional fields of specificity for each incident.
Forcing the System’s Hand
We stop talking to the perpetrator to show the system a clean, undisputed break.
When you show a detective or an HR director a log that says, “On Oct 12, I told them to cease all contact. Since then, they have contacted me 14 times via three different platforms,” you have provided a closed loop. It removes the ability to dismiss the perpetrators behavior as a misunderstanding.
You aren’t a participant in a dispute.
You are a witness to a pattern of behavior. This shift in perspective is one of the core principles of the overall Definitive Defense Protocol. You stop defending your character and start presenting a structured, verifiable record.
By refusing to confront them, you have maintained the high ground, kept your fight-or-flight response manageable, and built a wall of paper that the predator can no longer climb over without being seen for exactly what they are.
The Conformed Documentation Standard:
The Difference
⚠️ Documentation is not “Journaling.” Most people start with feelings rather than facts. The Paper Trail Primer is built on technical standards to help you help forensic investigators, auditors, and other professionals in an investigation.
| The “Good Person” Method (Failure) | Conformed Documentation | |
| Storage | Loose notes, screenshots, and memory | Centralized evidence log with a Table of Contents |
| Timing | Written days later when overthinking and remunerating starts | Contemporaneous Entry (logged while the facts are fresh) |
| Tone | Emotional, accusatory, and frantic | 19 Fields of Specificity (Unemotional and objective) |
| Pattern | Viewed as “Isolated Incidents” | Correlation Mapping (could prove intent and escalation) |
| Verification | “Trust me, I’m telling the truth.” | Cross-Referenced Metadata (Weather, Witnesses, GPS) |
| System View | You are a “nuisance” or “complainer” | Higher chance of being a credible witness with a verifiable timeline |
Case Studies: Failure vs. Victory
Case Study A: The “Friendly” Neighbor
A woman was being harassed by a neighbor who would stand at the edge of her property staring into her windows. She called the police three times. Each time, the police said, “He’s on his own property, there’s nothing we can do.”
- The Shift: She started documenting each incident on an Entry Log Form. She logged 42 instances over two months, including specific times he followed her to the grocery store.
- The Result: With a 10-page log in hand, the sheriff and her lawyer couldn’t claim it was a neighbor dispute. The log proved a pattern that started crossing the definition of stalking in her jurisdiction. Police reports were made, kept, and logged. Finally, a judge was able to offer her a protective order.
Case Study B: The Hidden Cost of Reporting a Safety Violation
A long-haul driver refused a trailer with a partially welded frame. The dispatcher told him to “stop being a princess” and then didn’t give him a load for three days. For the next month, his miles stayed below 1,200.
- The Shift: The driver used the Entry Log Form and the Paper Trail Table of Contents to record the mechanical failure and the dispatcher’s exact words. He then printed his settlement sheets showing the 60% drop in income, found the corresponding dates, and highlighted them.
- The Result: When he sat down with a labor attorney, he was able to hand over tangible data vs. “just a hunch.” The timeline, incidents, and results have been documented in an organized way. The company settled out of court because the verifiable data was easy to get to, easy to subpoena, and easy to cross-reference.
Defensive Decision Making: Your 5-Step Process
When the rules fail and the “good person” assumptions fall away, reclaim your space by following a protocol that helps you make good defensive decisions.
- Stop the impact of the adrenaline dump: The second you feel that knot in your stomach, your brain defaults to “fight-or-flight.” Open the Entry Log Form and ground yourself in the immediate, physical facts of your situation.
- Conduct an honest safety audit: Performing an honest audit about your current situation is the only way to gain clarity. Be honest about where the encroachment is happening. Are they getting through your front door, your smartphone, or your paycheck? Identify the actual breach (and any more possible personal targets) before trying to fix it.
- Contemporaneous logging: Do not trust your “later” self to remember the details. Log the incident the moment it happens, as soon as it is safe to do so. Memory is a liability under pressure. Written records don’t get rattled when answering questions posed by legal or law enforcement personnel. The information speaks for itself, letting everyone (including you if you or your loved ones believe you’re in denial) focus on the facts of what is or has been happening.
- Identify the “guise”: Strip away the excuses the system is using to ignore you. Whether they call it a “neighborhood dispute” or “slow freight,” name the lie so you can stop fighting the distraction and start shining light on the source.
- Build the correlation: Use your logs to try connecting the dots. Don’t just show the incident. Show the pattern that proves the “excuse” is a fabrication. When you prove that the “slow market” only applies to your truck, or the “public sidewalk” is only used at 2 a.m. to stare at your window, you stop sounding crazy and show that you’re logical and intend on proving what you’re saying is true.
When finished, you’re going to have absolutely clarity, know exactly what your choices are (or where to start looking for them), and feel safer than have in a very long time.
Physical Defense Key Takeaways
- The System is Reactive. You must provide the data that shows (not just tells) there is a problem.
- Locks are for doors; Logs are for people. Physical security is incomplete without documentation.
- Retaliation is a Guise. Companies try to make you quit through pressure in alternate ways vs. overtly firing you. Document the financial result with bank statements and pay stubs, not just the argument.
- Contemporaneous writing is king. Logs written at the time of the event carries several times more weight than summaries written weeks later.
Frequently Asked Questions (FAQs)
Won’t keeping a log make me paranoid?
No. It does the opposite. It forces the energy produced by your adrenaline out of your head and onto the paper so it doesn’t rest in your body, creating havoc. It allows you to see if a threat is real or if you’re just stressed. Data provides clarity. Silence provides anxiety.
What if the police won’t look at my logs?
Most patrol officers won’t. But detectives, lawyers, and judges could. Your log is proof for every single person that touches your case that events are taking place in your life, that they keep happening, and that you’re taking the time to document it each time it does.
Can my company fire me for keeping these records?
In the CDL world, you’re required to report issues to the proper authorities, whether that be the shop, your terminal leader, or the police. Keeping logs of your pre-trip, post-trip, or in-trip inspections, your miles, your hours of service, and your shipping documents is part of your job. They can’t fire you for being organized or for applying that same level of detail to their infractions or abuses.
I pay for a professional home security service. Isn’t that good enough?
Yes and No. It can be a little better than having your own because they have databases, a team, and system of operation in place. Help could reach you faster in some situations.
However, those same databases can crash or be hacked into. Maybe the video was too grainy to identify the face of the person who broke into your home. What happens to your evidence then?
Employees can become disgruntled and lie to you over the phone about the notes placed on your account. Think back to how many times this has happened in other companies you’ve done business with. One department doesn’t know, didn’t hear, or claim there are “no notes” or “No, that wasn’t mentioned in your account,” and it’s infuriating.
You are at their mercy, and the person you’re talking to, knows it.
If you want the best of both worlds while using a professional home security service as part of your overall physical defense plan or physical defense strategy, then pay for the service, understand their protocols inside and out, and document your interactions with them on the Entry Log Forms. Attach any email threads, support ticket reference numbers, and other identifying information about your issue.
Pay and document. Do both.
If anything happens on their end to your interactions or information, your paper trail backs you up, and gives legal professionals a starting point on which backed-up records to search for and obtain.
The Solution: Beyond DIY Documentation
You are tired. You are frustrated. You are fighting a system that feels like it’s rooting for the bad guy.
The Paper Trail Primer isn’t about “journaling” your feelings. It is a tactical weapon designed to close the gap between your reality and their evidence requirements. Stop letting administrative tactics or perpetrators from encroaching your space and robbing you of your peace.
You may have already been harmed in some way, but using these tactics, you prove they chose the wrong victim.